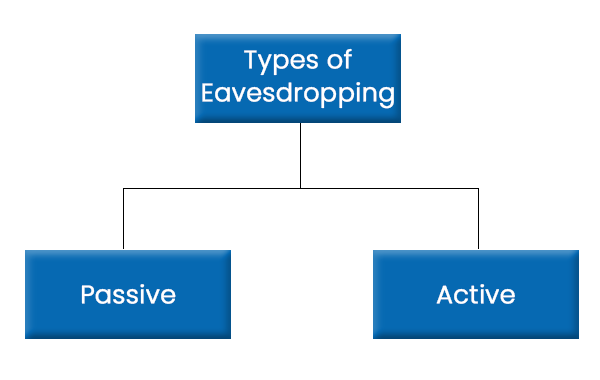
PDF) Defending Against Randomly Located Eavesdroppers by Establishing a Protecting Region | Octavia Dobre - Academia.edu
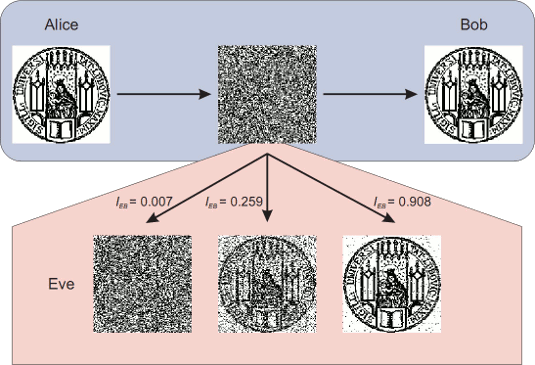
![PDF] Active Eavesdropping Detection Based on Large-Dimensional Random Matrix Theory for Massive MIMO-Enabled IoT | Semantic Scholar PDF] Active Eavesdropping Detection Based on Large-Dimensional Random Matrix Theory for Massive MIMO-Enabled IoT | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/6eaeb5847b258c8a1cfa351d3723ee49c0407531/3-Figure1-1.png)
PDF] Active Eavesdropping Detection Based on Large-Dimensional Random Matrix Theory for Massive MIMO-Enabled IoT | Semantic Scholar
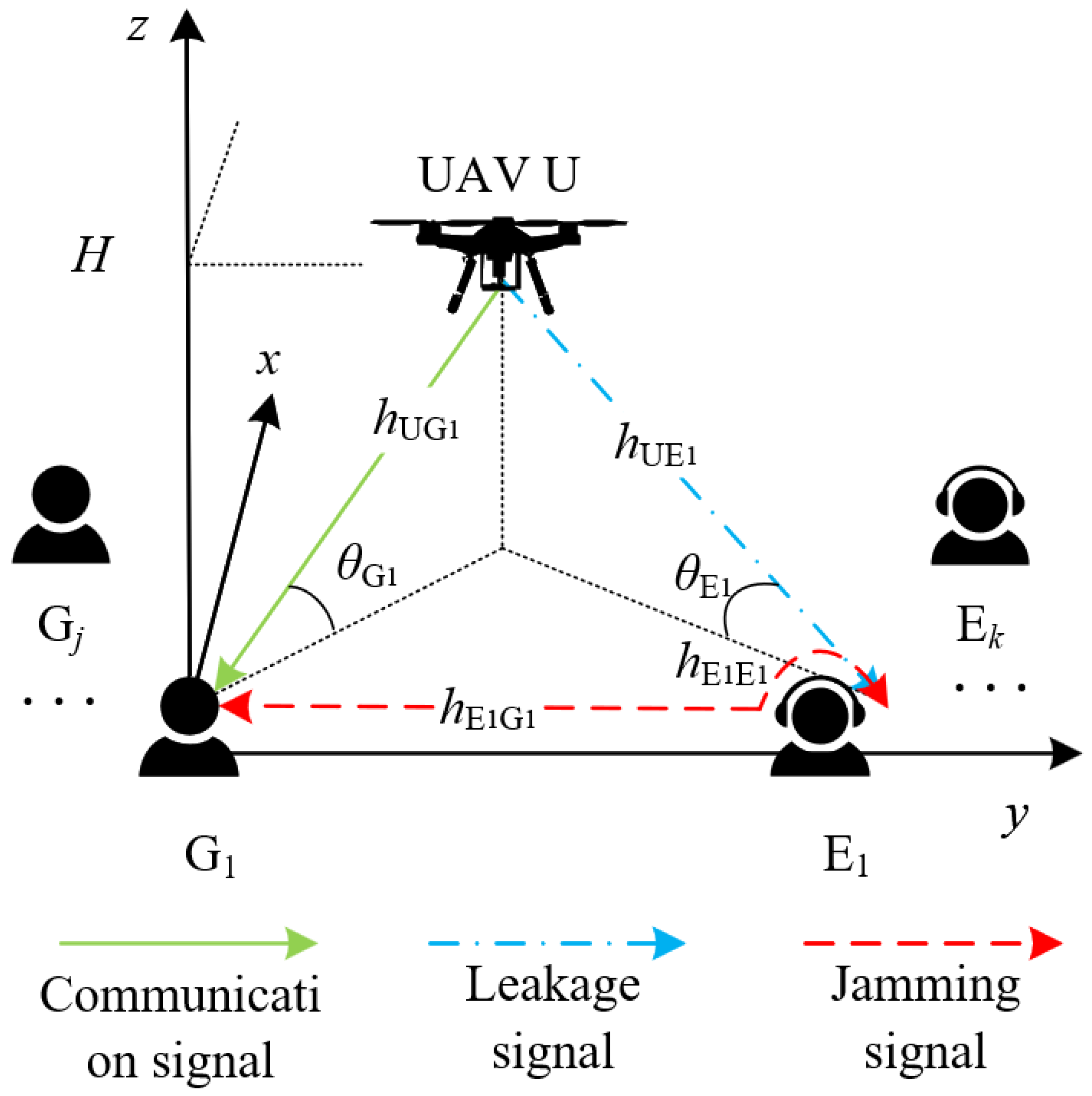
Drones | Free Full-Text | Safeguarding UAV Networks against Active Eavesdropping: An Elevation Angle-Distance Trade-Off for Secrecy Enhancement
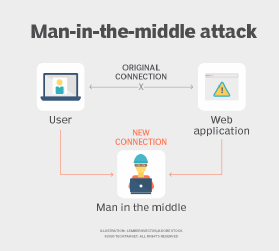
MITM attack. Man in the middle cyberattack, active eavesdropping example and unprivate online communication vector Illustration Stock Vector Image & Art - Alamy

Tech vansh - What is an Eavesdropping Attack? #ethicalhacking #hacking #kalilinux #cybersecurity #hackers #hack #hacker #linux #python #anonymous #technology #programming #security #infosec #ethicalhacker #developer #malware #pentesting #web #hacked ...

Mini Small Infrared Detecting Night Viewing Video Camera Detector Equipment Tool,active Alarm, Real-time Monitoring,anti-eavesdropping Detector, Anti- | Fruugo NO

An illustration of active eavesdropping in massive MIMO-based systems. | Download Scientific Diagram

Analysis and Validation of Active Eavesdropping Attacks in Passive FHSS RFID Systems | Semantic Scholar